Advertising on Twitter is challenging. Unlike the social media platform Facebook where ads can be targeted to reach your desired demographic and niche, ads on Twitter are shown to all users who are using the social media platform. This means that advertisers need to prioritize developing an ad design that is eye-catching while also following the best practices when the content of the chosen post is composed. In this blog, we will explore how advertising works on Twitter as well as provide useful tips for developing campaigns that are guaranteed success no matter what niche you represent.
Table of Contents
Promoted tweets
Promoted tweets are regular tweets that are purchased by advertisers in an attempt to reach a wider audience or generate more engagement from their existing followers. These Tweets are clearly labeled as “promoted” and advertisers pay Twitter for this placement. Promoted tweets generally work just the same as normal tweets and anyone who sees them can engage by retweeting, liking, and replying. This form of advertisement is great because you can reach more people who might be interested in your business or brand. Additionally, you can use these promoted tweets for a call to action on Twitter which is an effective way to promote any engaging content and drive website traffic. Of course, you can always use different tools to get yourself out there. For example, you can take advantage of the tools available to get Twitter likes on Earthweb, which is not advertising, but it can greatly affect your growth.

Promoted accounts
Instead of promoting only one tweet, you can instead promote your entire Twitter account. This form of an advertisement specifically targets users who do not follow your account which will help you grow your Twitter following. When you choose to promote your account, it will show up on the timeline of potential followers and the ad will also include suggestions on who to follow. The ad will also indicate with a label that this is a promotion and overall is an effective way to expand the reach and boost awareness of your brand or business.
See also:
Promoted trends
Trending topics on Twitter are a collection of the most popular hashtags and topics that are being used on the app in real-time. Twitter users can now interact with a promoted trend the very same way they would interact with a regular trend. The difference is that promoted trends will have the standard “promoted” label attached for targeted users. When a trend is promoted it also occupies the top spots on the “trends for you” section on the explore tab and on the timeline. If a user decides to click on the promoted trend, they will see search results for that particular topic with any promoted tweets from your business or brand attached at the top. This is an excellent way to boost visibility, brand awareness and attract followers.
How to start advertising?
To begin advertising on the Twitter platform you need to follow these steps;
- Set up a Twitter ads account.
- Choose your advertising goal.
- Set up your ad group.
- Select your target audience.
- Select your ad placement.
- Your campaign is ready to launch.
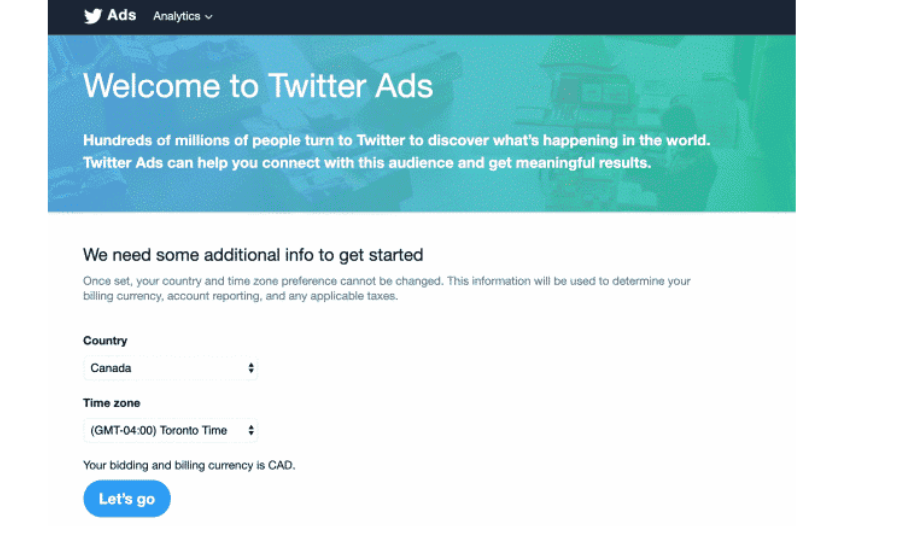
When selecting your goals, you must determine if you want to boost awareness by expanding reach or video views, etc. you will also need to decide how much you are willing to pay for the Twitter ad. There is no minimum budget for those who want to advertise which allows you to choose how much or how little you are prepared to pay. It’s also important to note that for your first ad campaign, you should stick to one ad group, and then as you get more familiar and comfortable with Twitter ads, you can divide your campaign into different categories that will each target different audiences. Don’t rush this process and make sure you understand every step. It shouldn’t be too time-consuming.
When it comes to advertising on social media, people typically think about Instagram first however, Twitter offers a comprehensive list of advertisement options for businesses and brands. These promoted tweets, accounts, and trends will enable you to reach a wider audience which will, in turn, grow your following and expose your business or brand to more people. Twitter is an open and diverse space so no matter what you choose to advertise, there will be a niche well suited for you.

