If you are wondering who Hunter Schafer is? Additionally, what transformation she underwent and Hunter Schafer before transformation etc. Then, this writing is going to answer all such queries of yours. Moreover, we all are well of the fact that nowadays, transgender, LGBTQ community, and bisexual all such words are very common to hear. Earlier there used to be a taboo on these words. Also, no one discussed these topics openly. But the scenario has changed a lot. People accept the LGBTQ community, who earlier considered them “not a part of society.” Alsmarellaoutlet pasante kondom 24h-bottle ovyescarpe ovyeshop 24bottlesclima saldigeox geoxoutlet nike ispa 270 nike ispa 270 lingerie super sexy loevenichhut corinne abbigliamento sexy 24bottlesclima mandarinaduckoutlet o, many activists support the LGBTQ community, fight for their rights, and hold many pride parades to show support. To the reader’s knowledge, Hunter Schafer is one of the LGBTQ activists. To know more about her life, career, and other personal information, Dive into the article!!
Table of Contents
Road to know about Hunter Schafer

To begin with, Schafer is an American LGBTQ rights activist, actress, and model. She was born on 31st December 1998 in Trenton, New Jersey. Teen Vogue in 2017 listed 23 years old Hunter Schafer in the “21 Under 21” list. This is because of her activism against the Public Facilities Privacy and Security Act of North Carolina. To the reader’s knowledge, Hunter made her acting debut in 2019 when she played the role of a transgender school student named Jules Vaughn in Euphoria, the HBO television series. Moreover, she will play the role of Tigris Snow in The Hunter Games: The Ballad of Songbirds and Snakes in 2023. Let’s dive further to know more about her early life and parents.
Hunter Schafer Early Life
New Jersey-born Schafer was born to Katy and Mac Schafer. Also, Hunter has three siblings. Her two sisters and a brother are younger than Hunter herself. Moreover, when it is about her early life, her father is a Presbyterian minister. Moreover, her family usually moved between congregations and churches in Arizona, New Jersey, and then finally to North Carolina. It was the time of Schafer’s High School when she protested against “The North Carolina Public Facilities Privacy & Security Act. Moreover, during her high school junior, Hunter was considered a prosecutor against the bill in the “Carcaño v. McCrory” lawsuit. However, Hunter was on the list of semi-finalists in her senior year for the “U.S. Presidential Scholars Program.”
See also:
In addition to that, Hunter did her graduation from Needham B. Broughton High School. However, she was transferred and then completed the “High School Visual Arts program in 2017 at the North Carolina School of Arts. However, Hunter planned to attend a different college named “Central Saint Martins.” It is an arts college situated in London, England. But, later on, she prorogued her enrollment to focus on her career after the completion of high school.
Explore the Career!!
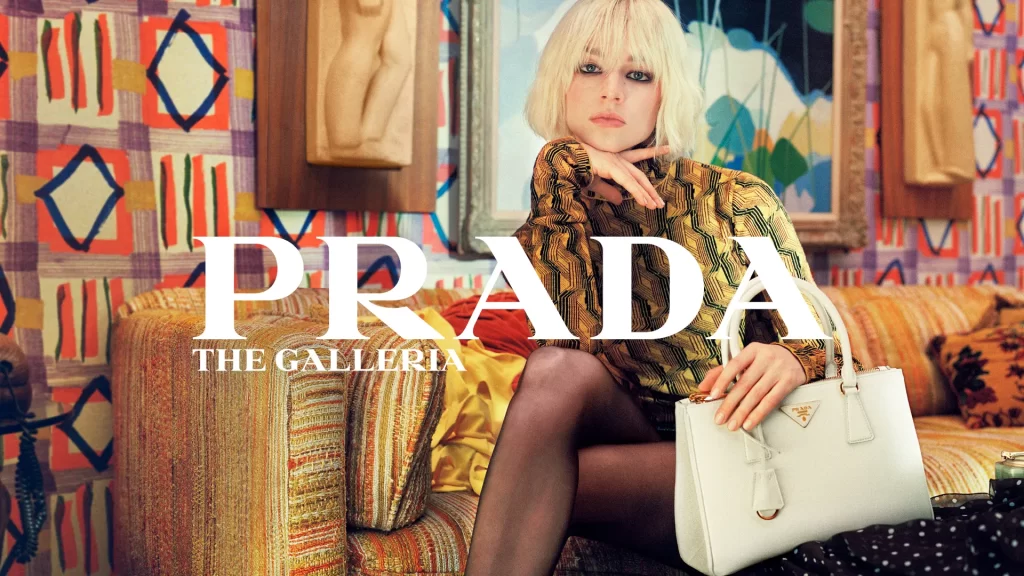
To the reader’s knowledge, Schafer developed an interest in acting and modeling from an early age. The famous “Leonardo DiCaprio so much inspired her.” So, Schafer started working for her passion just after she graduated from the University of North Carolina. Moreover, Schafer modeled for the famous fashion show named ‘New York Fashion Week” for the first time. Later on, she got various opportunities from big brands like Prada, Calvin Klein, Gucci, Tommy Hilfiger, Dior, and Helmut Lang. Additionally, she also modeled for Rick Owens, Thierry Mugler, Vera Wang, Coach, Versus Versace, Maison Margiela, Emilio Pucci, Erdem, Ann Demeulemeester, and various other big fashion houses.
Hunter Schafer Career in acting

Now the turning point had come in the life of Miss Hunter Schafer when she got the opportunity to roleplay in the HBO television series “Euphoria.” She gained immense popularity due to her main role in the series. The series was based on the legendary Israeli mini-series. And the show focuses on high school students who navigate several teenage issues like love, family, sex, substance abuse, identity, and friendship. In this drama series, Schafer played the role of a transgender student named Jules Vaughn. Jules is involved with a teen “Ruby Rue Bennet, a drug addict. They both share a turbulent relationship. Moreover, the series cast other actors like Zendaya, Eric Dane, Maude Apatow, Storm Reid, and Algee Smith. In addition to all these co-actors, Euphoria’s cast also includes Barbie Ferreira, Jacob Elordi, Angus Cloud, Alexa Demie, Sydney Sweeney, and various other actors.
During her budding career as an actress, Hunter also voiced for the English version of the Japanese anime movie “Belle.” The film was based on science fantasy and was released quite recently. Besides that, Schafer also played the role of “Ruka-Chan” Watanabe in the famous film ‘Beauty and the Beast.” We all are very well acquainted with the flick that is based on a French fairytale
A Moment of Pride!!
Apart from her acting and modeling involvement, Schafer co-wrote the episode with Sam Levinson (show creator) and is a co-executive producer in Euphoria. The very reason behind her involvement as a co-writer reflects her experience in the show story as well as in her character. Without a doubt, she did a commendable job. To the reader’s surprise, Primetime Emmy Awards were criticized due to omitting Schafer from the nominations. Additionally, these nominations omit various other transgender people actors along with her.
It was definitely a beat of pridefulness for Schafer when Queerty named Hunter on the list of 50 heroes in the glory of the 50th anniversary in June 2020 of the first LGBTQ Pride Parade. These heroes are known for “leading the nation toward equality, acceptance, and dignity for all people.” The moment of happiness did not end here for Hunter Schafer. She was then listed in the “100 emerging leaders who are shaping the future” list in 2021 by time. That time Zendaya, Euphoria’s co-actor, also wrote the tribute for her. Also, Schafer received various nominations during her career, including the Best Actor award in Short Awards, a nomination in GALECA, and by LGBTQ Entertainment Critics in the Rising Star of the Year list.
Who is Hunter Schafer Before Her surgery?

There are a lot of questions fans must have seen about Schafer’s sexuality. To the reader’s knowledge, there are a lot of websites that confirm her sexuality even though Schafer herself said in an interview that she is not” Cisgender.” If you are not aware of the term “Cisgender,.” Then, to the reader’s knowledge, it is a term used for the person who has the same gender at present, which was at the time of birth. As a matter of fact, at the time of her birth, Doctors confirmed that she was born male. But, presently, She is a transgender woman who underwent a transition in high school. It was the same time when she was diagnosed with gender dysphoria.
Once in an interview, Hunter Schafer stated, “I would like people to know that I’m not a cisgender because that’s not something that I am or I would feel like I am. Moreover, I’m proud to be a trans person”. In 2019 she tweeted that she was “closer to what you might call a lesbian.”
If you have ever heard a transgender story. You must have heard from their mouth that they did not fit in the skin that they are in. Moreover, earlier their family also didn’t understand what exactly they were going through. Also, they did not support their children. But as time passed, it changed. Now, they are supporting their children with their choices. Because love has no caste, gender, or color.
Similarly, Schafer, throughout her life, searched for femininity via art and fashion. And finally went for gender change surgery. And the cherry on top is that modeling helped Schafer get people’s attention on her views. Additionally, it also deconstructs the vision of gender.
Hunter Schafer’s relationship status
We all know that celebrities face a lot of rumors when it comes to their personal life. Similarly, Schafer did. Fans are talking about Schafer’s relationship with Dominic Fike. It is pretty obvious to talk as they both were seen together holding hands in a lunchroom in West Hollywood. Moreover, if we talk about their meeting. The two met during the shooting of Euphoria season 2. As a matter of fact, Dominic corroborated their relationship when he posted the kissing picture with Hunter as a belated birthday post. This picture posting incident happened just after a month after their apparent dinner date.

Moreover, they both made their red carpet debut in March at the “Vanity Fair Oscars party.” At that time, neither of them commented publicly about their affair. However, in an interview, Dominic confirmed that he is “in love” with his co-star Hunter Schafer. Henceforth, we can say that the rumors about which fans were talking are true. And both the stars dived deep into the ocean of love.
Now, it’s time to know about the net worth of Hunter Schafer before signing off. So, without any further delay. Let’s find out how much Hunter Schafer has in her pocket.
How much did hunter Schafer have in her pocket?
After facing so much discomfort in her skin, Schafer established herself quite well. Thus, if we talk about how much she has in her pocket. Then, to the reader’s knowledge, Hunter Schafer has a net worth of around 1 million USD. Moreover, Schafer’s annual income is $250,000. Without a doubt, most of the income came from brand endorsements. She advertises for various international MNCs.
Moreover, She is also a global ambassador of the makeup brand name SHISEIDO Skincare. Not only does her income part come from brands. But also from television series and fashion shows. Additionally, due to her name in the “21 under 21” list by teen Vogue. She got the opportunity for an interview with Hillary Clinton, former U.S. secretary of state and senator.
Hunter Schafer Wiki:-
| Hunter Schafer Wiki and Biography | |
| Real Name | Hunter Schafer |
| Profession | Actress, activist, and model |
| Age | 23 as in July 2022 |
| Birthdate | 31 December 1998 |
| Birthplace | Trenton, New Jersey |
| Nationality | American |
| Religion | Christianity |
| Famous for | She is famous for her role as a transgender school student in the HBO series Euphoria. And also as an activist along with the youngest plaintiff in Bathroom Bill. |
| Hobbies | Photography, Watching Movies and Horseback Riding |
| Height, Weight, and Body Measurements | |
| Height in Centimeters | 177 cm |
| Height in meters | 1.77 m |
| Height in Inches | 5 feet 10 inches |
| Weight in Kilograms | 65 kg |
| Weight in Pounds | 143 lbs |
| Body Measurements | |
| Bra Size | 34 |
| Waist Size | 28 |
| Hip Size | 34 |
| Eye Color | Blue |
| Hair Color | Blonde |
| Family and Relatives | |
| Father | Mac Schafer |
| Mother | Katy Schafer |
| Brother | 1 brother (Name Not Known) |
| Sister | 2 Sister (Name Not Known) |
| Affairs, Boyfriends, and Marital Status | |
| Marital Status | Unmarried |
| Boyfriend | Dominic Fike |
| Husband/ Spouse | Not available |
| Son | NA |
| Daughter | NA |
| Education and School, College | |
| Educational Qualification | Graduated |
| School | Needham B. Broughton High School |
| College/ University | North Carolina School of the Arts |
| Money Factor | |
| Net Worth | $1 million dollars |
| Salary as Judge | $250,000 USD |
| Contact Address | |
| House Address | Information Not Available |
| Phone Number | Not Known |
| Email Id | Not Known |
| Website | Not Known |
| Social Media | |
| @hunterschafer | |
| Hunter Schafer | |
| Not available | |
| Wikipedia | Hunter Schafer |
| IMDb | Hunter Schafer |
Final Words: Hunter Schafer Before
Now you all are quite aware of the life of Hunter Schafer before and after her transition. Not only did she manage to accept the fact that she is transgender. But also, she said it out loud and is proud of herself. It really mandates a lot of gutsiness to present ourselves as transgender in front of the cruel world.
I hope you like the article and find it useful for more updates on your favorite celebs. Please bookmark the page. And also, inform us in the comment box about which celebrity you want to know next. Till then, stay safe and hail reading!!